SAML¶
Go to Manage > Member Management > SSO Management > User SSO, select the SAML access type, and start adding an identity provider.
Start adding an identity provider¶
- Identity provider: A platform that provides identity management services, used to manage user identities and authentication information. Define a name here (❗️This name will serve as the IdP alias and appear on the single sign-on IdP selection interface. To ensure you can quickly locate the desired IdP for login, an appropriate name must be provided);
- Metadata document: The XML document provided by the IdP;
- Remarks: Custom description information used to record relevant details about the identity provider;
- Access restrictions: Verify whether the email domain suffix matches the configured domain. Only emails that match will have permission to access the SSO login link. For users logging in for the first time, a Guance member account can be dynamically created without needing to be pre-created in the workspace;
-
Role assignment: Assign roles to SSO accounts logging in for the first time. Accounts that are not logging in for the first time are not affected;
- If SAML mapping is enabled in the workspace, role assignment will prioritize the mapping rules.
-
Session persistence: Set the inactivity hold time and maximum hold time for SSO login sessions.
For details on role permissions, refer to Role Management.
Obtain Entity ID and assertion address¶
After successfully adding the identity provider, click the Update button on the right to obtain the Entity ID and Assertion Address. Once the corresponding SAML configuration is completed according to the identity provider's requirements, it will be ready.
| Field | Description |
|---|---|
| Login Address | The Guance SSO login address generated based on the metadata document. Each login address is limited to accessing one workspace |
| Metadata | The Guance SSO metadata file generated based on the metadata document |
| Entity ID | The entity ID for Guance SSO login generated based on the metadata document. Used to identify the service provider (SP) in the identity provider (IdP), such as Guance |
| Assertion Address | The assertion target address for Guance SSO login generated based on the metadata document. Used by the identity provider (IdP) to invoke and complete single sign-on |
Session persistence¶
When configuring SSO single sign-on, you can set a unified login hold time for enterprise members logging in via SSO, including the "Inactivity Login Session Hold Time" and "Maximum Login Session Hold Time".
- Inactivity Login Session Hold Time: Supports a range of 180 to 1440 minutes, with a default value of 180 minutes.
- Maximum Login Session Hold Time: Supports a range of 0 to 7 days, where 0 means never timeout, with a default value of 7 days.
Example
After updating the SSO login hold time:
- For members already logged in: Their login session expiration time remains unchanged.
- For newly logged-in members: The latest login hold time settings take effect.
For example:
- When initially configuring SSO, the inactivity session expiration time is set to 30 minutes. If member A logs in at this time, their inactivity session expiration time is 30 minutes.
- The administrator then updates the inactivity session expiration time to 60 minutes. Member A's inactivity session expiration time remains 30 minutes, while member B, who logs in after this change, will have an inactivity session expiration time of 60 minutes, and so on.
Login verification¶
- Log in via email to access the Guance SSO page: https://auth.guance.com/login/sso;
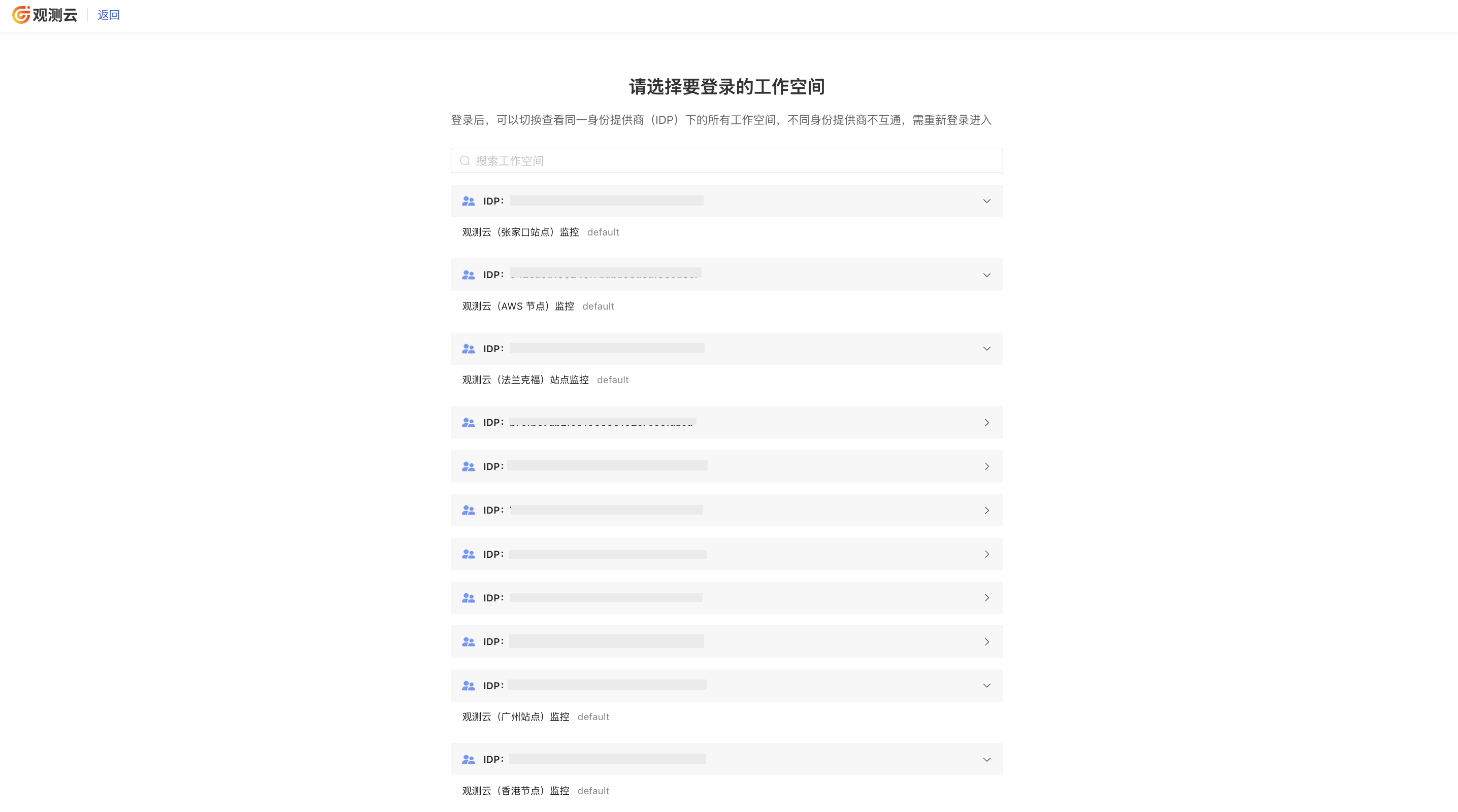
- Enter the email address configured during SSO setup and select the IDP of the workspace you wish to log into;
- After successful authentication, you will be redirected to the workspace selection interface;
- Log into that address;
- Enter your username, password, and other required information;
- Login successful.
Note
- If the workspace has role mapping enabled, but the current user does not match any role or role mapping is disabled, the message "No access permission" will be displayed;
- After an identity provider is deleted from the workspace, users will not see unauthorized workspaces when selecting SSO login.